Briefly Introduction to the Vulnerability
On December 19, 2018, SandboxEscaper released details about another zero-day vulnerability in Microsoft Windows with PoC. This vulnerability, if successfully attack, can be used to bypass restricted DACL of files and let the attacker to gain arbitrary access to file's content.
According to SandboxEscaper's explanation, this vulnerability comes from MsiAdvertiseProduct function.
The MsiAdvertiseProduct function generates an advertise script or advertises a product to the computer. The MsiAdvertiseProduct function enables the installer to write to a script the registry and shortcut information used to assign or publish a product. The script can be written to be consistent with a specified platform by using MsiAdvertiseProductEx. - Microsoft [4]
Calling MsiAdvertiseProduct function leads to copying of files by installer service (MsiInstaller) as SYSTEM which can be abused by creating time to check to time to use (TOCTOU) race condition type to bypass validation. Because this vulnerability is based on race condition so there is a chance that it might not be successful.
If it is successful, the destination file will always be readable which lead to its type (arbitrary file read vulnerability) as you can see in the following video.
This PoC also work on Windows 7 and Windows Server 2012/R2.
Therefore, there are records about using MsiInstaller in an Application Event log. So we can use those records to detect if someone tries to use this vulnerability whether success or not.
Event ID "1040" with "MsiInstaller" Source
In the Application Event log, there is event ID 1040 on source MsiInstaller that record an activity when Windows Installer has been started.
Description of normal event ID 1040 on MsiInstaller will contain information in two forms.
- Beginning a Windows Installer transaction: <full path to .msi file>. Client Process Id: <process_id>. [5]
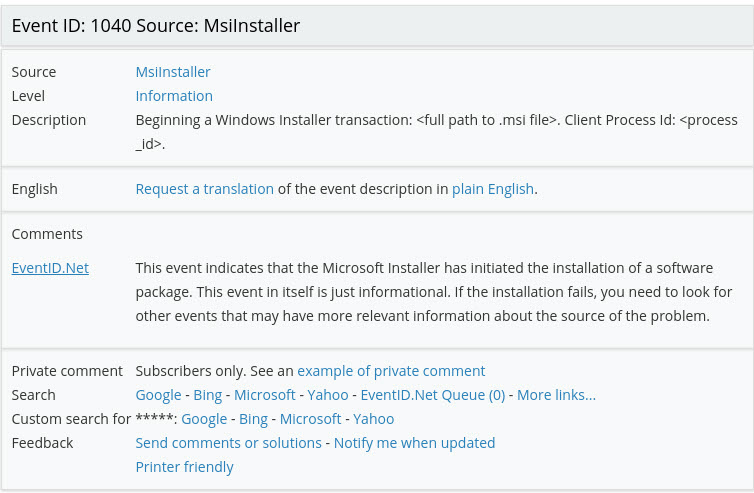
Event ID "1040" with "MSIInstaller" as source. Full path of MSI file will be shown in this form.
- Beginning a Windows Installer transaction: {GUID}. Client Process Id: <process_id>. [6]
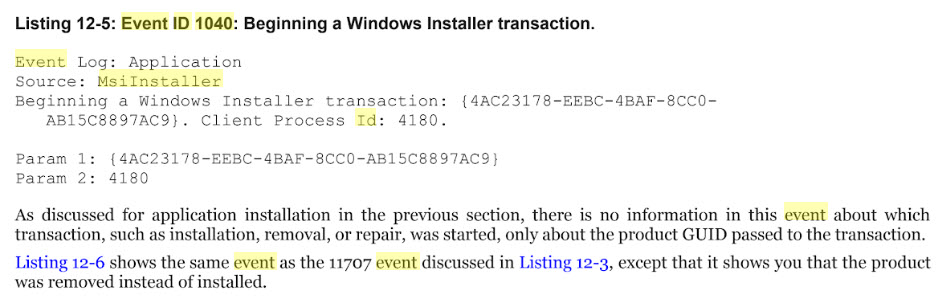
Event ID "1040" with "MSIInstaller" as source. GUID will be shown in this form.
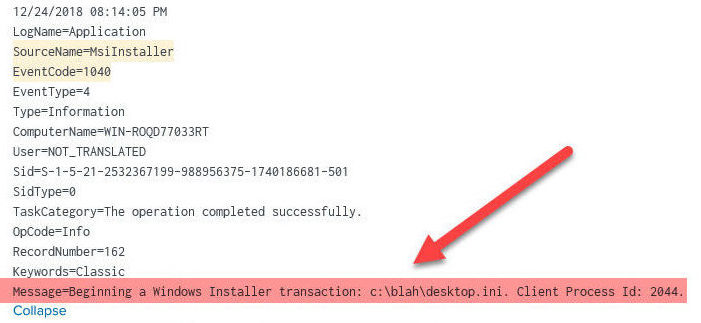
If you use Sandboxescaper’s POC to abuse MsiAdvertiseProduct function and attack arbitrary file read vulnerability. Whether success or not, this activity will be recorded in the Application Event log in abnormal form. For example, if you use ReadFile.exe with desktop.ini, event ID 1040 with MsiInstaller as event source will record desktop.ini in its description as follows.
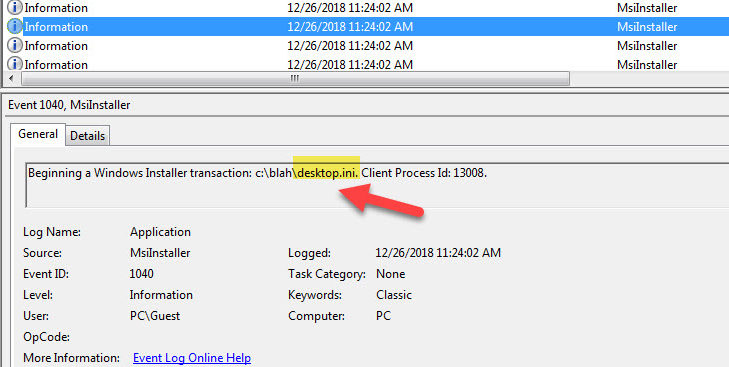
Event ID 1040 on MsiInstaller source with desktop.ini in its description.
Searching for Intention
As a Splunk user, we can use the following indicator to build simple query to check whether there is anyone try to use this vulnerability, by searching for the event in abnormal form (event ID 1040 on MsiInstaller and doesn't contain .msi or {GUID}
"EventCode=1040" AND (NOT ".msi") AND (NOT "}") AND "SourceName=MsiInstaller"
Reference
- http://sandboxescaper.blogspot.com/2018/12/readfile-0day.html
- https://www.zdnet.com/article/researcher-publishes-poc-for-new-windows-zero-day/ and https://www.bleepingcomputer.com/news/security/windows-zero-day-poc-lets-you-read-any-file-with-system-level-access/
- https://docs.microsoft.com/en-us/windows/desktop/api/msi/nf-msi-msiadvertiseproducta and http://www.eventid.net/display-eventid-1040-source-MsiInstaller-eventno-10770-phase-1.htm
- https://books.google.co.th/books?id=nEJRDwAAQBAJ&pg=PT503&lpg=PT503&dq=event+id+1040+msiinstaller

You must be logged in to post a comment.